The breadth and abundance of exploits for unknown vulnerabilities sets group apart.
DAN GOODIN - 3/18/2021, 6:18 PM - From: ARS Technica
A team of advanced hackers exploited no fewer than 11 zero-day vulnerabilities in a nine-month campaign that used compromised websites to infect fully patched devices running Windows, iOS, and Android, a Google researcher said.
Not over yet
On Thursday, Project Zero researcher Maddie Stone said that, in the eight months that followed the February attacks, the same group exploited seven more previously unknown vulnerabilities, which this time also resided in iOS. As was the case in February, the hackers delivered the exploits through watering-hole attacks, which compromise websites frequented by targets of interest and add code that installs malware on visitors’ devices.
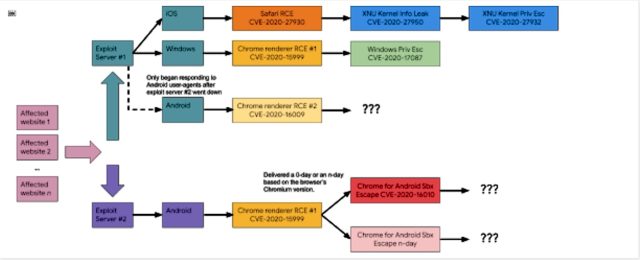
In all the attacks, the watering-hole sites redirected visitors to a sprawling infrastructure that installed different exploits depending on the devices and browsers visitors were using. Whereas the two servers used in February exploited only Windows and Android devices, the later attacks also exploited devices running iOS. Below is a diagram of how it worked:
The ability to pierce advanced defenses built into well-fortified OSes and apps that were fully patched—for example, Chrome running on Windows 10 and Safari running on iOS—was one testament to the group’s skill. Another testament was the group’s abundance of zero-days. After Google patched a code-execution vulnerability the attackers had been exploiting in the Chrome renderer in February, the hackers quickly added a new code-execution exploit for the Chrome V8 engine.
